Installing a VM Agent
Each VM agent (VMA) has its own ID, certificate, and pre-shared key. The VMA ID must be unique, meaning that duplicate agents (that is, agents with the same ID) are not permitted. It is recommended that you use unique certificates and master passwords with each VMA. See below for installation details.
Installation
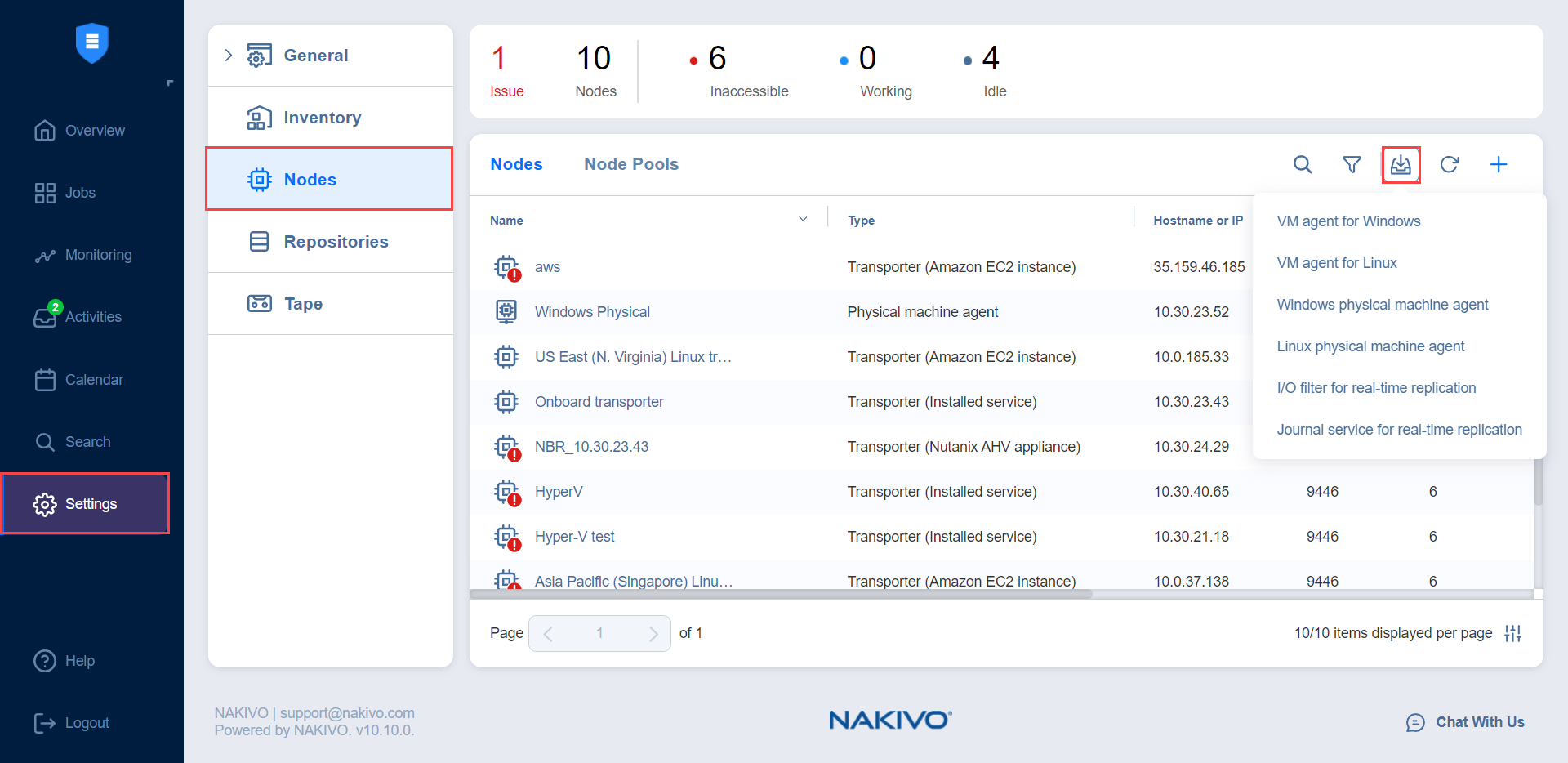
You can download the VM agent (VMA) installer files from the application UI. To do this, go to Settings > Nodes, click the Download button, and select the needed OS.
Installation is done via the command line and requires you to set up a master password with a minimum length of 5 characters. Note that you cannot install a VMA on a machine on which a Transporter is installed, and vice versa. See command examples below:
-
Windows: installer.exe --cert C:\certificate.pem -p ExamplePassword --eula-accept
-
To confirm installation success, check Control Panel > Programs & Features
-
Installation result is logged in C:\install.log
-
-
Linux: installer.sh -s 9445 --cert /tmp/certificate.pem -p ExamplePassword --eula-accept
-
To confirm installation success, run the systemctl status nkv-bhsvc command.
-
Installation result is logged in /tmp/nkv-install.log
-
After installing the VM agent, proceed as described in Using a VM Agent.
Removal
Removing a VM agent in the product UI does not remove it from the VM. Removing VM agents is only possible by uninstalling them from the VM. See uninstallation details below:
-
Windows: Run Uninstall NAKIVO Backup & Replication Agent, located in the NAKIVO folder within Programs.
-
Linux: Run the /opt/nakivo/agent/uninstall command.
Certificate
Installed VM agents (VMAs) may use a CA-signed certificate or a self-signed certificate. After successful installation of the VMA, local copies of the provided certificate for VMA installation are automatically removed.
Multiple CA certificate chains are not supported. CA certificates must be placed in the Director installation folder. These certificates are trusted automatically by the Director.
If a CA-signed certificate is not provided, the VMA automatically generates a self-signed certificate.